Analysis of Windows Vulnerability Scan
こんにちは, OSSのVulsへContributeしているMaineK00nです.
今回は, OSSで公開されたWindowsの脆弱性検知をVuls祭り#7のスライドをもとにして解説していきたいと思います.
また, Vuls祭り#7@YouTubeで当日の発表の様子を見ることが出来ます.
以前, Windows Vulnerability Scanというタイトルで投稿した記事では, 更新プログラムの置き換えや, マシンの更新プログラムの適用状況を調べる方法について紹介しているため, 併せて読むと理解が深まるかもしれません.
VulsでのWindows脆弱性検知 ステータス
はじめに, 少し簡単にVulsでのWindows対応ステータスをまとめました.
- ローカルスキャン, リモートスキャン(SSH), サーバスキャンすべて使える
- リモートスキャンを使えば, Windows → Linux, Linux → Windowsのスキャンもできる
- サーバスキャンなら, スキャン対象のマシンにVulsバイナリの用意や, SSHサーバの設定は必要なく, systeminfo.exeの結果をリクエストするだけでよい
- 脆弱性DBを用意すれば, オンライン, オフラインに関わらず検知可能である
利用している脆弱性情報
Microsoft Security Research Center: MSRCが提供しているCVRF1とBulletinSearch2 3を利用している.
基本的に, これらの脆弱性情報には, 各脆弱性とそれを修正するKBIDがプロダクトごとに記述されており, Microsoft Edgeのような製品は, KBIDではなく修正バージョンが記述されることもある.
また, 更新プログラムの置き換え情報はCVRF, BulletinSearch以外に, オフラインスキャンで利用されるWsusscn2.cab4やWindows Update Catalog5からも収集している. CVRFやBulletinSearchの情報だけでは脆弱性に紐づくKBの前後しか分からないため, 置き換え情報の構成には不十分なのである.
Vulsでは, これらのデータソースを vulsio/windows-vuln-feed リポジトリで収集し, 管理している. 脆弱性情報や更新プログラムの置き換え情報で誤りや漏れがある場合はこちらのリポジトリにissueで報告してもらえると助かります.
また, vulsio/windows-vuln-feed リポジトリで管理するデータを利用するために, vulsio/gost リポジトリを提供している.
簡単な使い方を紹介する.
1 |
$ git clone https://github.com/vulsio/gost.git |
脆弱性検知の方針
CVE-2022-34708の定義を見る.
Windows 10 Version 21H2 for x64-based SystemsでKB5016616が未適用であるならば, CVE-2022-34708は影響すると判断できる.
これを機械的に処理するには, NameとArticleの情報を対象のマシンから集める必要がある.
1 |
{ |
OSを特定する
脆弱性情報に沿ったOS名を特定する必要がある.
そのため, Vulsでは集めた情報からOS名を構成する.
例えば, 以下のsysteminfo.exeの結果でOS名を構成する手順を紹介する.OS Version: 10.0.19044からMajor.Minor Version: 10.0, Build: 19044ということがわかる.OS Configuration: Member WorkstationからWindows Serverではないようだ.
Major.Minor Versionが10.0であるWorkstationはWindows 10かWindows 11となる.
また, Build Numberから, Windows 10 Version 21H2まで特定できる.
そして, System Type: x64-based PCを合わせて, Windows 10 Version 21H2 for x64-based Systems という名前を構成できる.
1 |
Host Name: DESKTOP |
Vulsでは, 4つのOSを特定する方法を用意している.
registryは他の3つの方法と異なり, Major.Minor.Build.UBRまで分かる.
ただし, registryは記事執筆当時では, リモートスキャンではSSH接続越しに実行することに失敗しているため, ローカルスキャンのみとなっている.
- registry(HKEY_LOCAL_MACHINE\Software\Microsoft\Windows NT\CurrentVersion, HKEY_LOCAL_MACHINE\System\CurrentControlSet\Control\Session Manager\Environment) (local scan only)
- Get-ComputerInfo
- Get-WmiObject Win32_OperatingSystem
- systeminfo.exe
インストールされているパッケージを調べる
記事執筆当時のVulsは, インストールされているパッケージを次のようにして調べている.
1 |
$ Get-Package | Format-List -InputObject $Packages -Property Name, Version, ProviderName |
インストールされているパッケージの結果から, 記事執筆当時のVulsでは, Microsoft Edgeのみ脆弱性情報を追跡している.
CVRFやBulletinで定義されるプロダクト名とインストールされているパッケージ名が一致するかどうかを確認しなければならないことなど課題がある.
更新プログラムの適用状況を調べる
Windows 10以前の更新プログラムはMonthly RollupとSecurity Onlyの2種類が提供されていました。Windows 10以降は累積更新となっている.
以前, 記事を投稿した際にあるKBからの置き換えをMicrosoft Update Catalogをもとに調べると, 次のようになっていた.
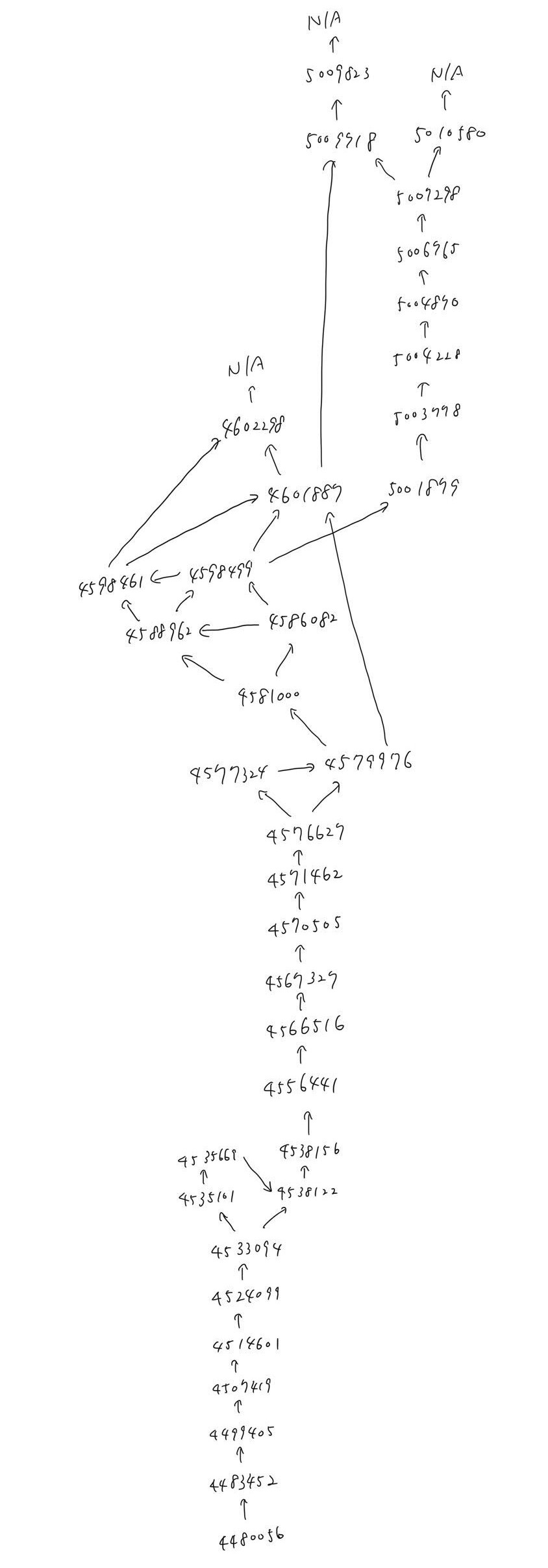
これを vulsio/windows-vuln-feed で提供している置き換え情報の形式で表現すると次のようになる.
1つ途切れると, 最新のKBまで展開出来ないということが起きる.
そのために, vulsio/windows-vuln-feed では機械的に対応できる手法をいくつか実装して, 対応しているが, それでも置き換え情報は途絶えてしまうことがある. そのために, 以下のようなJSONを手動で書いて, 置き換え情報を表現することも出来るようにしている. もし, 置き換え情報の不足に気がついた方はissueやpull requestをください.
1 |
[ |
これまでに, 更新プログラムの置き換えがどのように表現されるかを考えました.
未適用な更新プログラムは, 適用済みの更新プログラムから置き換え情報を辿れば, 求めることができそうである.
Vulsでは, 更新プログラムの適用状況を以下の手法で集めている.
記事執筆当時のVulsでは, 3. IUpdateSearcher::Search はSSH越しで動作させることが難しいことからローカルスキャンのみ, 6. systeminfo.exe はサーバモードのみとなっている.
- Get-Hotfix
- Get-Package -ProviderName msu
- IUpdateSearcher::Search6 (local scan only)
- IUpdateSearcher::QueryHistory7
- Major.Minor.Build.UBR まで取得できている場合, Vulsで定義済みのOSの累積更新プログラムから検索
- systeminfo.exe (server mode only)
OSの脆弱性を検知
OSがWindows 10 Version 21H2で, 適用済みKBがKB5012117, KB4562830, KB5003791, KB5007401, KB5012599, KB5011651, KB5005699ということから, 画像を見るとKB5016616が未適用なKBの一つであることが分かる.
1 |
Host Name: DESKTOP |
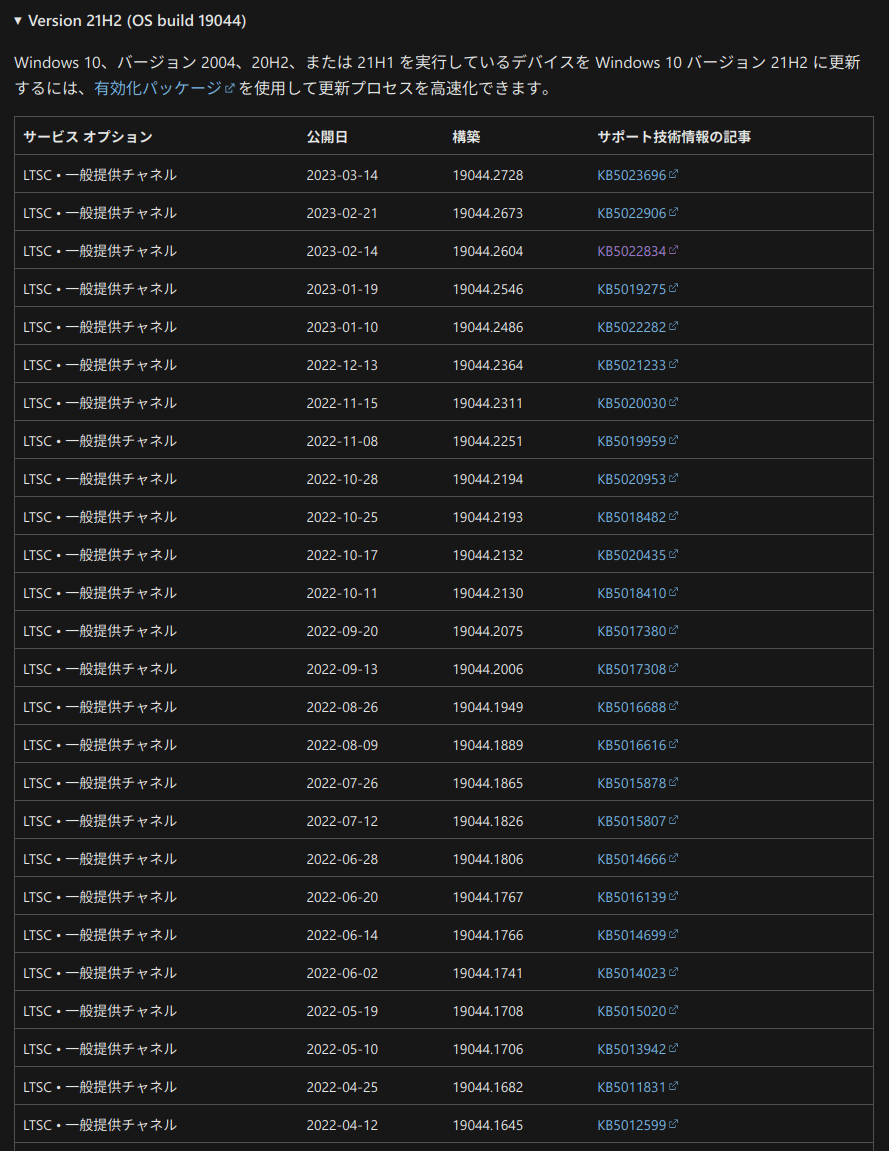
Reference: https://learn.microsoft.com/en-us/windows/release-health/release-information
CVE-2022-34708はOSがWindows 10 Version 21H2 for x64-based Systemsのとき, KB5016616によって修正されるとあるので, このマシンはCVE-2022-34708が影響すると判断する.
1 |
{ |
Windows 10以前の更新プログラムは2種類で提供していたという説明をしたが, 脆弱性情報でも2つ記述されている.
KB5016681が未適用であっても, KB5016683が適用済みの場合, この脆弱性は修正済みであると判断する.
1 |
{ |
また, このようにKBsが定義されていない脆弱性は, 更新プログラムでの修正が提供されていないものか, 更新プログラム以外での対応が必要なものが多い.
1 |
{ |
OS以外のProduct: Microsoft Edgeでの脆弱性検知
Microsoft Edgeの検知を考えてみる.
CVRFでのMicrosoft Edgeに関する脆弱性をいくつか抜粋した.
Get-Packageで取得できるパッケージ名はMicrosoft Edgeであるにも関わらず, CVRF上にはMicrosoft Edge (EdgeHTML-based) on <OS Name>, Microsoft Edge (Chromium-based) in IE Mode on <OS Name>, Microsoft Edge (Chromium-based)の3パターンあり, BulletinSearchにはMicrosoft Edge on <OS Name>で定義されている.
さらに, 修正に関する記述も様々で, CVE-2021-26411は修正したKBID, CVE-2021-41351は修正したKBIDとFixed Version, CVE-2023-24892はFixed Versionのみとなっている.
また, CVE-2021-42308はFAQに96.0.1954.29と書いてあり, Fixed Versionには96.0 1954.29とあるが, Releses Notesを見ると, Fixed Versionは96.0.1054.29のようである.
CVE-2020-16044とCVE-2020-1195に至っては, KBIDもFixed Versionも記述はない. ただし, FAQに書いてある.
記事執筆当時のVulsでは, EdgeのバージョンからEdgeHTML-basedか, Chromium-basedを判断し, 候補となるMicrosoft Edgeのパッケージ名を求め, それらのパッケージ名に関する脆弱性情報を取得して, KBIDがある場合, Fixed Versionがある場合でそれぞれで対応している.
しかし, OS以外のプロダクトでKBを利用しないケースの脆弱性検知は, 脆弱性情報を整備する段階で非常に難しい.
1 |
<vuln:Vulnerability Ordinal="47"> |
Windows対応をもっと安定させるために, 皆様へのお願い
まとめ
この記事では, Vuls祭り#7で使用したスライドに沿って, VulsでのWindows対応について解説しました.
Linux/FreeBSDと同じ感覚でWindowsもスキャンできるようになりました.
Windowsのスキャンを安定させるためにも, 皆様からのフィードバックをお待ちしております.
最後に, Microsoft Security Research Centerの方へこの記事が届いたならば, より実用的な脆弱性情報が提供できるように何かお手伝いをさせてください, お願いします.
- 1.https://api.msrc.microsoft.com/cvrf/v2.0/swagger/index ↩
- 2.https://download.microsoft.com/download/6/7/3/673E4349-1CA5-40B9-8879-095C72D5B49D/BulletinSearch.xlsx ↩
- 3.https://download.microsoft.com/download/6/7/3/673E4349-1CA5-40B9-8879-095C72D5B49D/BulletinSearch2001-2008.xlsx ↩
- 4.https://catalog.s.download.windowsupdate.com/microsoftupdate/v6/wsusscan/wsusscn2.cab ↩
- 5.https://www.catalog.update.microsoft.com/Home.aspx ↩
- 6.https://learn.microsoft.com/en-us/windows/win32/api/wuapi/nf-wuapi-iupdatesearcher-search ↩
- 7.https://learn.microsoft.com/en-us/windows/win32/api/wuapi/nf-wuapi-iupdatesearcher-queryhistory ↩
